War Driving, Why and How - PowerPoint PPT Presentation
1 / 53
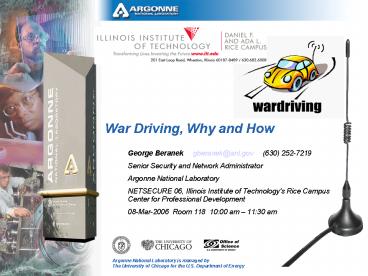
Title: War Driving, Why and How
1
War Driving, Why and How
- George Beranek gberanek_at_anl.gov (630)
252-7219 - Senior Security and Network Administrator
- Argonne National Laboratory
- NETSECURE 06, Illinois Institute of Technology's
Rice Campus Center for Professional Development - 08-Mar-2006 Room 118 1000 am 1130 am
2
What is War Driving?
- war driving n. A computer cracking technique that
involves driving through a neighborhood with a
wireless-enabled notebook computer and mapping
houses and businesses that have wireless access
points. - Wardriving is driving around a city searching for
the existence of Wireless LAN (802.11) Networks.
It's locating and logging wireless access points
while in motion. Often, this task is automated
using dedicated wardriving software and a GPS
unit. - Wardriving was invented by Peter Shipley and is
now commonly practiced by hobbyists, hackers and
security analysts worldwide. - "Wireless technology sets data free from the
physical confines of wire which also means that
controlling who receives the data is problematic.
Peter Shipley, the director of labs at OneSecure,
told me about his new hobby of driving around
Silicon Valley and picking up networks on his
laptop. war driving is replacing war dialing in
the wireless age." Carole Fennelly, Unix
Insider, December 2000
3
Why War Drive?
- Do tech managers know where all their wireless
LAN access points (AP) are? Since they can be
plugged into a LAN and stashed almost anywhere,
even by users, they can be a challenge to manage
internally. Meanwhile, strangers can be
discovering them be "war driving," cruising
around with a wireless-enabled laptop seeking
wireless LANs that can be entered and explored.
"IBM Tool Targets Wireless 'War Driving',"
e-Business Advisor, August, 2002t - From a technical perspective War Driving can be
very interesting, White Hat Hacking - As a hobbyist War Driving is both FUN technically
challenging. - Bandwidth Stealers (warez sharing, etc...)
- Anonymity Seekers (legal and illegal motives)
- True Black Hat Hackers
4
Hardware
- Required
- A portable computer (laptop / palmtop)
- Dell Latitude D810 (ear bud recommended)
- A compatible built in or pcmcia Wireless NIC
- external antennae (omnidirectional /
unidirectional) - A GPS http//www.cantenna.com/
- http//www.deluoelectronics.com/
- Optional (but very very cool)
- Linksys WRT54G Wireless Router / Access Point
5
Netstumbler vs. Kismet (Windows vs. Linux)
- Netstumbler http//www.netstumbler.com/
- Runs on Windows XP
- Great for a quick war-walk / war-drive or a quick
vulnerability assessment (rogue access point
detection) or coverage / interference testing on
an unprotected network, but.... - Netstumbler sends out 802.11 Probe Request
frames for SSID Any providing no real
advantage, but making it easily detectable. - Netstumbler does not sniff.
- Kismet http//www.kismetwireless.net/
- Runs on Linux / Unix (client ported to Windows)
- Kismet puts your wireless NIC into RFMON mode and
does Passive Scanning - Kismet will discover and report the IP address,
netmask, and default gateway as well as the SSID
of no ssid sites if possible. - Kismet sniffs and records packets for later use
with Ethereal, AirSnort, AirCrack, etc... - Kismet's intrusion detection feature will detect
many probing / attack fingerprints including
Netstumbler
6
Basic Software
- Packages that you'll need
- gpsd GPS (Global Positioning System) service
daemon http//gpsd.berlios.de/ - kismet Wireless 802.11b monitoring tool
http//www.kismetwireless.net/ - Packages that you'll want
- Ethereal network traffic analyzer
http//www.ethereal.com/ - gpsdrive Car navigation system
http//gpsdrive.kraftvoll.at/ - festival general speech synthesis
http//www.cstr.ed.ac.uk/projects/festival/ - MySQL database package http//www.mysql.com/
- xgps gui client for the GPS service daemon
http//gpsd.berlios.de/xgps.html - wifi-radar gui for managing Wi-Fi profiles
http//www.bitbuilder.com/wifi_radar/ - Other Packages
- Airsnort WLAN sniffer http//airsnort.shmoo.com/
- Aircrack wireless WEP cracker
http//www.wirelessdefence.org/Contents/AircrackMa
in.htm - Dsniff sniffs network traffic for cleartext
insecurities http//www.monkey.org/dugsong/dsnif
f/
7
Setup
- Install NIC, GPS, and Software Paclages
- Compile RFMON mode NIC driver kernel modules if
necessary - Setup the MySQL database
- mysql -u root -p lt /usr/share/gpsdrive/create.sql
(This will add a user gast / gast) - Edit /etc/kismet/kismet.conf for your NIC and
configuration. - sourceipw2915,eth1,BuiltIn,6
- sourceorinoco,eth2,BuiltIn,6
- sourcecisco,eth2,BuiltIn,6
- sourcekismet_drone,192.168.108.13501,drone
8
Execution
- Start the GPS daemon
- ps -ef grep -i gps Kill gpsd -F
/var/run/gpsd.sock if present - dmesg grep -i usb check to make sure your
GPS has associated with a port - ln -s /dev/ttyUSB0 /dev/gps gpsd -K -f
/dev/gps ps -ef grep -i gps - make sure that mysqld is running ps -ef grep
-i sql , /etc/init.d/mysql restart if not - make sure festival is running ps -ef grep -i
sql , festival --server if not - Add localhost to xhosts xhost xhost
localhost xhost - Start xgps xgps -speedunits mph -altunits ft
- Make sure that no kismet components are running
ps -ef grep -i kismet, kill if present - Start Kismet kismet
- Start gpsdrive gpsdrive
- Start wifi-radar wifi-radar
- Now Do Your War Drive!
9
Kismet can be integrated with MySQL, GPSDrive,
and SNORT
10
War Driving with Kismet http//www.kismetwireless
.net/
- Synthesized voice announces discoveries. (Great
while driving, but an ear bud makes it even
better) - Real Time Commands
- s Sort network list
- l Show wireless card power levels
- i Detailed information about selected network
- r Packet rate graph
- a Statistics
- d Dump printable strings
- e List Kismet servers
- m Toggle muting of sound and speech
- c Show clients in current network
- H Return to normal channel hopping
- x Close popup window
- h Help (Many Other Controls)
11
Mapping the results
- gpsmap -v -l ssid -L 0 -G -t -D -p -r -a -e -k
-S 2 Kismet-date-numbers
12
Power
- gpsmap -v -l ssid -L 0 -G -t -D -p -r -a -e -k -S
2 Kismet-date-numbers.
13
Power
- gpsmap -v -l ssid -L 0 -G -t -D -p -r -a -e -k -S
2 Kismet-date-numbers.
14
IIT Rice Campus with Intel ipw2915 mini pci
internal
- gpsmap -v -l ssid -L 0 -G -t -D -p -r -a -e -k -S
2 Kismet-date-numbers.
15
IIT Rice Campus with Orinoco Gold pcmcia card and
external antenna
- gpsmap -v -l ssid -L 0 -G -t -D -p -r -a -e -k -S
2 Kismet-date-numbers.
16
IIT Rice Campus with Linksys WRT54G OpenWRT
Kismet Drone
- gpsmap -v -l ssid -L 0 -G -t -D -p -r -a -e -k -S
2 Kismet-date-numbers.
17
IIT Rice Campus aggregate of all 3 war drives
- gpsmap -v -l ssid -L 0 -G -t -D -p -r -a -e -k -S
2 Kismet-date-numbers.
18
ShoniBrook I
- gpsmap -v -l ssid -L 0 -G -t -D -p -r -a -e -k -S
2 Kismet-date-numbers.
19
ShoniBrook II
- gpsmap -v -l ssid -L 0 -G -t -D -p -r -a -e -k -S
2 Kismet-date-numbers.
20
ShoniBrook III
- gpsmap -v -l ssid -L 0 -G -t -D -p -r -a -e -k -S
2 Kismet-date-numbers.
21
1840
- gpsmap -v -l ssid -L 0 -G -t -D -p -r -a -e -k -S
2 Kismet-date-numbers.
22
2648
- gpsmap -v -l ssid -L 0 -G -t -D -p -r -a -e -k -S
2 Kismet-date-numbers.
23
FCC Berwyn
- gpsmap -v -l ssid -L 0 -G -t -D -p -r -a -e -k -S
2 Kismet-date-numbers.
24
Argonne 200
- gpsmap -v -l ssid -L 0 -G -t -D -p -r -a -e -k -S
2 Kismet-date-numbers.
25
Argonne 300
- gpsmap -v -l ssid -L 0 -G -t -D -p -r -a -e -k -S
2 Kismet-date-numbers.
26
Unidirectional Antenna War Walk to eliminate
clutter
- gpsmap -v -l ssid -L 0 -G -t -D -p -r -a -e -k -S
2 Kismet-date-numbers.
27
ShoniBrook GPSDrive with Kismet (friends mode)
- gpsmap -v -l ssid -L 0 -G -t -D -p -r -a -e -k -S
2 Kismet-date-numbers.
28
ShoniBrook GPSDrive with MySQL
- gpsmap -v -l ssid -L 0 -G -t -D -p -r -a -e -k -S
2 Kismet-date-numbers.
29
IIT Rice Campus GPSDrive with Kismet
- gpsmap -v -l ssid -L 0 -G -t -D -p -r -a -e -k -S
2 Kismet-date-numbers.
30
IIT Rice Campus GPSDrive with MySQL
- gpsmap -v -l ssid -L 0 -G -t -D -p -r -a -e -k -S
2 Kismet-date-numbers.
31
IIT Rice Campus using Orinoco NIC and
Unidirectional Cantenna
- gpsmap -v -l ssid -L 0 -G -t -D -p -r -a -e -k -S
2 Kismet-date-numbers.
32
A War Walk using Windows XP
- gpsmap -v -l ssid -L 0 -G -t -D -p -r -a -e -k -S
2 Kismet-date-numbers.
33
NetStumbler War Walk of IIT Rice Campus
- gpsmap -v -l ssid -L 0 -G -t -D -p -r -a -e -k -S
2 Kismet-date-numbers.
34
Results of Kismet IIT Rice Campus War Walk (No
GPS indoors)
- Network 1 "rice_wireless" BSSID
"00C049A97BB1" infrastructure 06
10.0.0.67 - Network 2 "rice_wireless" BSSID
"00C049A9755A" infrastructure 06 10.0.0.0 - Network 3 "rice_wireless" BSSID
"00C049A9A0FF" infrastructure 06
10.0.0.173 - Network 4 "rice_wireless" BSSID
"00C049A9758E" infrastructure 01 10.0.0.1 - Network 5 "voiplab" BSSID "004096A1111D"
infrastructure 03 WEP - Network 6 "tsunami" BSSID "000D288E56DE"
probe 00 - Network 7 "rice_wireless" BSSID
"00C049A9757A" infrastructure 11
216.47.135.65 - Network 8 "cuwireless.net" BSSID
"02026F21E91A" ad-hoc 11 169.254.233.26 - Network 9 "rice_wireless" BSSID
"00C049A97580" infrastructure 11
192.168.1.3 - Network 10 "rice_wireless" BSSID
"00C049A97588" infrastructure 11
10.0.0.101 - Network 11 "BlackHole" BSSID "001217087458"
infrastructure 01 WEP - Network 12 "wirelessR624" BSSID
"000F3D3B42A8" infrastructure 06 WEP - Network 13 "2WIRE501" BSSID "000D72D5C399"
infrastructure 06 WEP - Network 14 "linksys" BSSID "0013100550AE"
infrastructure 06 - Network 15 "2WIRE937" BSSID "00149578BEB1"
infrastructure 06 WEP - Network 16 "ltno ssidgt" BSSID "001217E4CE22"
probe 00 - Network 17 "2WIRE085" BSSID "000D72A20DF9"
infrastructure 06 WEP - Network 18 "Aegus 243" BSSID "00146C458DE6"
infrastructure 11
35
Map Sources GPS maps are available from many
sources
- Mapblast http//www.slhonline.org/MapBlast!
Mapblast!.htm http//www.mapblast.com/ - MapPoint http//mappoint.msn.com/
- Terraserver http//www.terraserver.com/
http//terraserver.microsoft.com/ - Tiger Census http//tiger.census.gov/cgi-bin/mapb
rowse-tbl - FreeGIS http//www.freegis.org/
http//www.freegis.org/browse.en.html - NASA satellite topology maps ftp//mitch.gsfc.nas
a.gov/pub/stockli/bluemarble/ - USGS http//www.usgs.gov/
- Netstumbler data can be plotted at a number
of websites http//www.wifimaps.com/
36
Data Analysis (/var/log/kismet/Kismet-Mar-03-2006
-10.dump)
- Kismet's .dump files can be read and analyzed by
Ethereal, AirSnort, AirCrack, etc... - Kismet
37
Data Analysis
- AirSnort load pcap file Kismet-Feb-15-2006-3.dum
p
38
Data Analysis
- AirCrack Kismet-Feb-15-2006-2.dump
- aircrack Kismet-Feb-15-2006-2.dump
39
Linux on the Linksys WRT54G
- History
- The WRT54G was released in 2003 in anticipation
of the 802.11g standard. - In June 2003 some folks on the Linux Kernel
Mailing List sniffed around the WRT54G and found
that its firmware was based on Linux components.
Because Linux is released under the GNU General
Public License, or GPL, the terms of the license
obliged Linksys to make available the source code
to the WRT54G firmware. As most router firmware
is proprietary code, vendors have no such
obligation. It remains unclear whether Linksys
was aware of the WRT54Gs Linux lineage, and its
associated source requirements, at the time they
released the router. But ultimately, under
outside pressure to deliver on their legal
obligation under the GPL, Linksys open sourced
the WRT54G firmware in July 2003. - With the code in hand, developers learned exactly
how to talk to the hardware inside and how to
code any features the hardware could support. It
has spawning a handful of open source firmware
projects for the WRT54G that extend its
capabilities, and reliability, far beyond what is
expected from a cheap consumer-grade router.
Seattle Wireless is generally credited as being
the first to upload new firmware to the WRT54G.
You can now actually run snort or kismet right on
your wireless router.
40
Linksys Firmware Replacements
- There now exists plethora of firmware
replacements for the WRT54G, such as - Sveasoft (no longer free) http//www.sveasoft.com/
- Wifi-Box https//sourceforge.net/projects/wifi-box
- BatBox http//www.batbox.org/wrt54g-linux.html
- These distributions can provide a lot of
additional functionality - Radio Transmit power adjustment
- Antenna selection
- Iptables filtering / Shorewall firewall
- Snort intrusion detection
- Telnet, SSH, local caching DNS, SNMP daemons
- Kismet Drone
- With the right replacement firmware, it can do
what youd only expect to be able to on a
commercial-grade router costing several times as
much BUT it can be difficult to find a firmware
that contains exactly the functionality that
you're looking for.
41
OpenWRT http//openwrt.org/
- The OpenWRT firmware takes a completely different
approach, turning your WRT54G into a complete
generalized interactive Linux system including
package (ipkg list) management. It is not based
on Linksys code at all. - Some notable features are the ability to
telnet/SSH to your router, install software such
as Snort, Kismet, Mini-Sendmail, and Iptables,
and create and control VLANs for every Ethernet
port on the device. - By default, OpenWrt's installation emulates the
normal Linksys firmware functionality. This means
that although you installed OpenWrt, your router
still acts as a wireless access point and switch.
(nvram show more) - OpenWrt obeys common networking conventions,
taking advantage of route, ifconfig, and
/etc/resolv.conf. - One of the great things about OpenWrt is its use
of iPKG, a tiny package management system
inspired by Debian's APT. With iPKG, installing
packages, such as tcpdump, is simple as running a
command like ipkg install tcpdump. Use ipkg
update and ipkg list to see what add-on software
is available. - You could use the WRT54G as a repeater or a
bridge. Create a wireless distribution system
(WDS) or a mesh network. Run a VPN server or a
VoIP server or a managed hotspot with a RADIUS
server. Manage bandwidth use per protocol.
Control traffic shaping. Support IPv6. Boost
antenna power. Remotely access router logs.
Operate the router as a miniature low-power PC,
running a variety of Linux applications. (UART
hardware mod)
42
http//192.168.108.11840/
- http//192.168.108.11840/cgi-bin/webif.sh
43
http//192.168.108.11840/cgi-bin/webif/wireless-c
onfig.sh
- http//192.168.108.11840/cgi-bin/webif.sh
44
http//192.168.108.11840/cgi-bin/webif/ipkg.sh
- http//192.168.108.11840/cgi-bin/webif.sh
45
Wireless intrusion detection using stationary
Kismet drones
- Kismet will provide alerts based on fingerprints
(specific netstumbler versions, other specific
attacks) and trends (unusual probes, excessive
disassociation, etc). Kismet focuses on the
802.11 (layer 2) network layer, and provides
integration via named pipes with layer3 IDS
systems such as Snort. - You can create inexpensive Kismet drone(s) using
WRT54G Wireless Routers and place them
strategically at your facility. A single Linux
system can act as the Kismet client for all of
these drones. In this way your wireless
installation can be continuously and
inexpensively monitored. Logs can even be
intelligently parsed for the appearance of rogue
access points with perl, swatch, etc.
46
Turn your Wireless Laptop / Desktop into an
Access Point
- By building your own Access Point on a Linux
server you can - Run an iptables firewall to protect your network
- Set up intrusion detection
- Build a captive portal
- Build a web caching server
- Actually you can do ALMOST ANYTHING!
- The ability to turn you laptop into a WAP can
come in very handy at times. It can overcome the
disadvantages of ad-hoc mode. It can also be
used to spoof an existing AP to attack / audit a
wireless installation. - What is actually necessary to achieve access
point functionality is to get your wireless NIC
into MASTER mode or to emulate this mode.
iwconfig wlan0 essid myAP mode master - This can be accomplished through the use of
enhanced driver software depending upon your
NIC's chipset hostap for Prism / cisco Aironet
, Hermes AP for Orinoco cards , madwifi for
Atheros , etc.
47
Specialized Linux Distributions
- If you're a Windows user who doesn't want to
install Linux then here's a live filesystem CD
distribution that will run everything you need
without touching your hard drive! - Knoppix STD (Security Tool Distribution)
http//www.knoppix-std.org/ - Contains http//www.knoppix-std.org/tools.html
- airsnarf rogue AP setup utility
- airsnort sniff, find, crack 802.11b
- airtraf 802.11b network performance analyzer
- gpsdrive use GPS and maps
- kismet 3.0.1 for 802.11 what else do you need?
- kismet-log-viewer manage your kismet logs
- macchanger change your MAC address
- wellenreiter 802.11b discovery and auditing
- patched orinoco drivers automatic (no scripts
necessary) - WARLINUX
- an easy form of Linux with Kismet for windows
users to try out https//sourceforge.net/projects/
warlinux/
48
Some Useful Commands
- iwconfig used to configure the basic operating
parameters of your wireless NIC. - cardctl - used to monitor and control the state
of PCMCIA sockets - iwlist - shows current parameters and available
access points - iwlist eth1 scanning - iwspy - shows quality of link parameters
- iwpriv allows you to configure private wireless
options specific to a single wireless driver.
49
Wireless Security Countermeasures
- Change Default Administrator Passwords (and
Usernames) - Turn on highest level WPA / WEP Encryption
- Change the Default SSID
- Enable MAC Address Filtering
- Disable SSID Broadcast
- Assign Static IP Addresses to Devices
- Position the Router or Access Point Safely
- Turn Off the Network During Extended Periods of
Non-Use - Use strong encryption like ssh for all
applications you use over the wireless network. - Encrypt wireless traffic using a VPN
- Keep firmware up to date
- Authenticate wireless users with protocols like
EAP - Create a dedicated segment for your Wireless
Network, and take additional steps to restrict
access to this segment - Regularly TEST the security of your wireless
network, using the latest Wardriving Tools. - Enable strict LOGGING on all devices and
routinely audit these logs. - Implement Wireless Intrusion Detection
50
Some Excellent References
- Linux Unwired by Roger Weeks
- A comprehensive and thoroughly useful treatment
of the basics of wireless Linux. - Great sections on Blue Tooth and IR for Linux
too. - http//www.oreilly.com/catalog/lnxunwired/
- WI-FOO The Secrets of Wireless Hacking Andrew
Vladimirov, Konstantin V. Gavrilenko, Andrei A.
Mikhailovsky - A much more advanced reference.
- The definitive guide to wireless attack and
defense. - http//www.wi-foo.com/
51
QUESTIONS?
- USE OPEN SOURCE http//www.opensource.org/
- UBUNTU http//www.ubuntu.com/
- FIREFOX http//www.mozilla.com/firefox/
- Open Office http//www.openoffice.org/
http//www.anl.gov/ - Argonne National Laboratory is located on 1,500
acres, 25 miles southwest of downtown Chicago.
52
Speaker Bio
- George Beranek began his professional computer
career in the early 1980's as a test engineer /
designer programming in HP Rocky Mountain Basic,
Pascal, Fortran, and C supplying intelligent
replacement for electro-mechanical test systems
as an independent contractor for Eaton
Corporation and Gould Research Center. In 1990
he transitioned into Unix System and Network
administration at Motorola where he eventually
headed a team of system administration and
networking professionals dedicated to quick
response and high performance technical computing
for their Cellular Infrastructure International
Systems Engineering Group during the peak of
their cellular boom. George is presently a
Senior Security and Network Administrator at
Argonne National Laboratory where he essentially
functions as an internal Linux consultant.
George received a BS in Electrical Engineering
and Computer Science from Northwestern
University's Technological Institute and a MS in
Electrical Engineering and Computer Engineering
from IIT. He is also a RedHat Certified Engineer
(RHCE) but of late has become passionate about
the Debian based Ubuntu Linux distribution.
George has been a member of the IEEE for the past
24 years.
53
- The Advanced Photon Source (APS) is the nations
brightest source of X-rays for research.




























![get⚡[PDF]❤ Hard Line: The Republican Party and U.S. Foreign Policy since World War II PowerPoint PPT Presentation](https://s3.amazonaws.com/images.powershow.com/10051196.th0.jpg?_=20240608115)
