Secure LAN Switching - PowerPoint PPT Presentation
1 / 36
Title:
Secure LAN Switching
Description:
Secure LAN Switching Layer 2 security Introduction Port-level controls Storm control Protected ports Private VLAN Port blocking Port security ACLs on switches – PowerPoint PPT presentation
Number of Views:106
Avg rating:3.0/5.0
Title: Secure LAN Switching
1
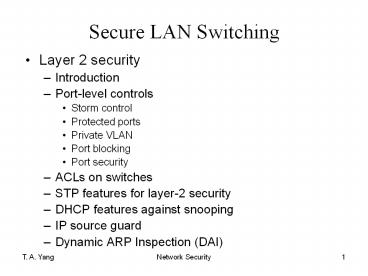
Secure LAN Switching
- Layer 2 security
- Introduction
- Port-level controls
- Storm control
- Protected ports
- Private VLAN
- Port blocking
- Port security
- ACLs on switches
- STP features for layer-2 security
- DHCP features against snooping
- IP source guard
- Dynamic ARP Inspection (DAI)
2
Switches and Layer 2 security
- Security of lower layer devices is important,
because some threats are initiated on Layer 2
rather than Layer 3 and above. - Example A firewall or a router cannot block a
compromised server on a DMZ LAN from connecting
to another server on the same segment. ? because
the connection occurs at Layer 2 - Focus of the chapter Cisco Catalyst series
switches (principles applicable to other types of
switches)
3
- Source http//www.cisco.com/ca/events/pdfs/L2-sec
urity-Bootcamp-final.pdf
4
Switch and Layer 2 security
- Sample L2 attacks and their mitigations
- See
- http//www.cisco.com/ca/events/pdfs/L2-security-Bo
otcamp-final.pdf - (local copy)
5
Port security
- A mechanism to restrict the MAC addresses that
can connect via a particular port of the switch - Allows a range of MAC addresses to be specified
for a particular port - Only frames with a right MAC address can go
through the switch. - Useful for preventing MAC address flooding
attacks - CAM overflow Content-Addressable Memory (aka.
associated memory) - CAM table stores information such as MAC
addresses available on physical ports, with their
associated VLAN params. - CAM table has fixed size.
- When a CAM table is full, the switch is unable to
create a new entry. - ? It forwards a received frame to all ports,
resulting in increased traffic and allowing the
attacker to examine all frames. - So, CAM overflow attacks may lead to subsequent
DoS and traffic analysis attacks (next slide)
6
MAC Address Flooding
7
MAC Address Flooding (cont.)
- Counter-measures
- Hard-coding the MAC addresses that are allowed to
connect on a port, or - Limiting the number of hosts that are allowed to
connect on a port - Example 5-1 approach 1 timed suspension
- Consolegt (enable) set port security 2/1 enable
- Consolegt (enable) set port security 2/1 enable
00-90-2b-03-34-08 - Consolegt (enable) set port security 2/1 shutdown
600 - Example 5-2 approach 2
- Consolegt (enable) set port security 3/2 maximum 20
8
IP permit lists
- Purpose To restrict higher layer traffic, such
asTelnet, SSH, HTTP, and SNMP, from entering a
switch - Allows IP addresses to be specified that are
allowed to send these kinds of traffic through
the switch - Command set ip permit enable
- Example 5-3
9
Protocol Filtering
- Purpose To limit broadcast/multicasts for
certain protocols - With Cisco Catalyst 5000 series of switches,
packets are classified into protocol groups - IP 2. IPX
- AppleTalk, DECnet, Banyan VINES 4. Other
protocols - A port is configured to belong to one or more of
these groups. - For each of the groups a port belong to, the port
is in one of the following states (for that
group) - On ? Receive all broadcast/multicast traffic for
that protocol - Off ? no broadcast/multicast traffic for that
protocol - Auto ? auto-configured port
- The port becomes a member of the protocol group
only after the device connected to the port
transmits packets of that specific protocol
group. - Once the attached device stops transmitting
packets for that protocol for 60 minutes, the
port is removed form that protocol group. - Example 5-4
10
Controlling LAN floods
- Attackers may cause frame flood (e.g., CAM
flooding), or send broadcast/multicast messages
to flood the LAN. - Counter-measures
- Protocol filtering
- Setting up threshold limits for
broadcast/multicast traffic on ports - Catalyst switches allow thresholds for broadcast
traffic to be set up on a per-port basis. - The thresholds can depend on either the bandwidth
consumed by broadcasts or the number of broadcast
packets being sent across a port. - Bandwidth consumed is a preferred measure.
(Why?) - Example Consolegt (enable) set port broadcast
2/1-6 75 - Other broadcast/multicast traffic is dropped when
the bandwidth consumed by broadcast/multicast
traffic reaches 75.
11
VLAN
- Virtual LAN
- Source http//www.cisco.com/en/US/tech/tk389/tk68
9/tsd_technology_support_protocol_home.html - Group of devices on one or more LANs that are
configured (using management software) so that
they can communicate as if they were attached to
the same wire, when in fact they are located on a
number of different LAN segments. - based on logical instead of physical connections
- extremely flexible
12
- Sample VLAN configurations
- Source http//www.cisco.com/en/US/products/hw/swi
tches/ps672/products_tech_note09186a0080093dca.sht
mlex1
13
- Multiple-VLAN Network
14
VLAN Trunking
- A trunk is an interface on a switch that can
carry packets for any VLAN. When packets get sent
between switches, each packet gets tagged, based
on the IEEE standard for passing VLAN packets
between bridges, 802.1Q. The receiving switch
removes the tag and forwards the packet to the
correct port or VLAN in the case of a broadcast
packet. - Be aware! VLAN Insecurity (by Rik Farrow)
http//www.rikfarrow.com/Network/net0103.html - VLANs make it possible to share a switch among
many LANs, by filtering and limiting broadcast
traffic. - But this form of isolation relies on software
and configuration, not the physical isolation
that security people like myself really like to
see.
15
Private VLANs
- An enhancement to some Cisco switches
- Traditional VLAN no layer 2 segregation of
devices of the same VLAN - ? So when one of the devices in a VLAN is
compromised, other devices on the same VLAN may
be compromised as well. - Purpose of private VLANs To allow restrictions
to be placed on the Layer 2 traffic of a VLAN.
16
Private VLANs
- Provides layer 2 isolation to quarantine hosts
from one another among ports within the same
PVLAN - Three types of private VLAN ports
- Promiscuous ports communicate with all other
private VLAN ports - Community ports communicate among themselves and
with their promiscuous ports - Isolated ports have complete Layer 2 isolation
from other ports within the same private VLAN
(e.g., Ethernet ports in hotel rooms)
17
(No Transcript)
18
Other security features in VLAN
- Port blocking
- When a packets MAC address can not be found in a
switchs MAC address table, the switch will
broadcast (flood) unknown unicast and multicast
traffic to all the ports in the same VLAN - This flooding can be blocked using port blocking
feature - Port filtering based on MAC address
- A set of MAC addresses are allowed to access a
port. - Packets with source MAC addresses outside the set
are dropped.
19
ACLs on Switches, 1/4
- Router ACL
- Switched virtual interfaces (SVI) are virtual
layer 3 interfaces. - Both standard and extended ACLs are supported on
SVI. - MAC ACL
- Aka Ethernet ACL
- Filters non-IP traffic using MAC address
filtering - Supports only inbound traffic
- mac access-list extended
20
ACLs on Switches, 2/4
- Port ACL
- Supported on physical layer 2 interfaces
- Supports only inbound traffic filtering
- Supports standard, extended, and MAC-extended
ACLs - Can filter both IP and non-IP traffic
- VLAN ACL (VACL)
- Aka VLAN map
- Filters all types of traffic bridged within a
VLAN or routed into or out of the VLAN - Examples next page
21
ACLs on Switches, 3/4
- VLAN ACL (VACL)
- Filters all types of traffic bridged within a VLAN
22
ACLs on Switches, 4/4
- VLAN ACL (VACL)
- Filters all types of traffic routed into or out
of the VLAN - Order of processing VACL for input VLAN, input
IOS ACL, Outbound IOS ACL, VACL for output VLAN
23
L2 security using STP features
- Spanning Tree Protocol (STP)
- Source http//www.cisco.com/en/US/tech/tk389/tk62
1/tsd_technology_support_protocol_home.html - prevents loops from being formed when switches or
bridges are interconnected via multiple paths. - implements the IEEE 802.1D algorithm by
exchanging BPDU messages with other switches to
detect loops, and then removes the loop by
shutting down selected bridge interfaces. - guarantees that there is one and only one active
path between two network devices.
24
Illustration of the STP
- http//en.wikipedia.org/wiki/Spanning_Tree_Protoco
l - Root ports vs Designated ports
25
The STP PortFast feature
- Source http//www.cisco.com/en/US/tech/tk389/tk62
1/technologies_tech_note09186a008009482f.shtml - STP configures meshed topology into a loop-free,
tree-like topology. - When the link on a bridge port goes up, STP
calculation occurs on that port. The result of
the calculation is the transition of the port
into forwarding or blocking state. The result
depends on the position of the port in the
network and the STP parameters. - This calculation and transition period usually
takes about 30 to 50 seconds. At that time, no
user data pass via the port. Some user
applications can time out during the period. - In order to allow immediate transition of the
port into forwarding state, enable the STP
PortFast feature. PortFast immediately
transitions the port into STP forwarding mode
upon linkup. The port still participates in STP.
So if the port is to be a part of the loop, the
port eventually transitions into STP blocking
mode.
26
The STP PortFast feature vulnerability
- Source http//www.cisco.com/en/US/tech/tk389/tk62
1/technologies_tech_note09186a008009482f.shtml - As long as the port participates in STP, some
device can assume the root bridge function and
affect active STP topology. - To assume the root bridge function, the device
would be attached to the port and would run STP
with a lower bridge priority than that of the
current root bridge. - This is a simple form of a denial of service
(DoS) attack on the network. The temporary
introduction and subsequent removal of STP
devices with low (0) bridge priority cause a
permanent STP recalculation.
27
The STP PortFast feature vulnerability
mitigation
- Source http//www.cisco.com/en/US/tech/tk389/tk62
1/technologies_tech_note09186a008009482f.shtml - The STP PortFast BPDU guard enhancement allows
network designers to enforce the STP domain
borders and keep the active topology predictable.
- The devices behind the ports that have STP
PortFast enabled are not able to influence the
STP topology. - At the reception of BPDUs, the BPDU guard
operation disables the port that has PortFast
configured.
28
L2 security using STP features
- BPDU Guard
- Bridge protocol data units (BPDU) are messages
exchanged btwn bridges using STP to detect loops
in a network. - BPDU Guard feature keeps the active topology
predictable and enhances switch network
reliability by enforcing the STP domain borders.
29
L2 security using STP features
- Root Guard
- A feature preventing a bridge in a particular
network from becoming the root bridge of that
network - e.g., enable Root Guard on service provider (SP)
side switch interfaces that connect to a
customer-side switch - ? If a switch outside the SP network becomes the
root switch, the interface is put in a blocked
state, and STP will select a new root switch. - spanning tree guard root
30
L2 security using STP features
- EtherChannel Guard
- Cisco EtherChannel technology is a trunking
technology based on grouping several full-duplex
802.3 Ethernet links to provide fault-tolerant,
high-speed links between switches, routers, and
servers. (source http//www.cisco.com/en/US/tech
/tk389/tk213/technologies_white_paper09186a0080092
944.shtml) - EtherChannel parameters must be the same on both
sides (e.g., btwn a switch and a connected
device) - When the switch detects an EtherChannel
misconfiguration, the EtherChannel Guard places
the switch interface in the error-disabled state
31
L2 security using STP features
- Loop Guard prevents alternative or root ports
from becoming designated ports, thus avoiding
loops - http//www.cisco.com/en/US/tech/tk389/tk621/techno
logies_tech_note09186a0080094640.shtmlloop_guard_
description - An STP loop is created when an STP blocking port
in a redundant topology erroneously transitions
to the forwarding state. - This usually happens because one of the ports of
a physically redundant topology (not necessarily
the STP blocking port) no longer receives STP
BPDUs. In its operation, STP relies on continuous
reception or transmission of BPDUs based on the
port role. The designated port transmits BPDUs,
and the non-designated port receives BPDUs. - When one of the ports in a physically redundant
topology no longer receives BPDUs, the STP
conceives that the topology is loop free.
Eventually, the blocking port from the alternate
or backup port becomes designated and moves to a
forwarding state. This situation creates a loop.
32
DHCP Snooping feature
- Protection from rogue DHCP servers
- Ports on a switch are divided into trusted and
untrusted ports. - DHCP clients and other hosts are connected to the
untrusted ports. - DHCP servers are connected to trusted ports.
- The switch maintains a DHCP binding database (aka
DHCP snooping table). - Incoming packets received on untrusted ports are
dropped if the source MAC address does not match
the MAC in the binding table.
33
IP Source Guard
- Protection from IP spoofing attacks when a host
tries to spoof and use the IP address of another
host - Any IP traffic coming into the interface with a
source IP address other than that assigned will
be filtered out.
34
Dynamic ARP Inspection (DAI)
- ARP (address resolution protocol) resolves a
32-bit IP address into a 48-bit Ethernet address,
using an ARP Table. - The ARP caches can be poisoned (an invalid ARP
entry is created in the table). - Result packet redirection to the attacker
- DAI locks down the IP-MAC mapping for hosts so
that the attacking ARP is denied and logged.
35
Setting up a secure Layer 2 switching environment
- Overview of Counter-measures
- Use VLANs to create logical groupings of devices
? Each of the groups may have different security
levels. - Disable unused ports, and place them in a VLAN
with no Layer 3 access. - Besides VLANs, other mechanisms must be used
(e.g., port security) - Separate devices should be used for zones at
different security levels. - Disable Layer 3 connection (e.g., Telnet, HTTP)
to the switch. - Disable trunking on ports that do not require it
(and place the trunk port in its own VLAN).
36
Need for other counter-measures
- How about attacks launched from hosts sitting on
a LAN? - In general, those hosts are considered as trusted
entities. - So it is difficult to stop a host when it becomes
an attacker. - Solution Make sure access to the LAN is secured.
- ? MAC address filtering (e.g., Ciscos port
security, DHCP)