Supervisory Special Agent R. David Mahon - PowerPoint PPT Presentation
1 / 48
Title:
Supervisory Special Agent R. David Mahon
Description:
PDD 63 Requires the FBI through the NIPC to: ... Coordinate FBI computer intrusion investigations ... CSI/FBI 2001 Computer Crime and Security Survey. Source: ... – PowerPoint PPT presentation
Number of Views:201
Avg rating:3.0/5.0
Title: Supervisory Special Agent R. David Mahon
1
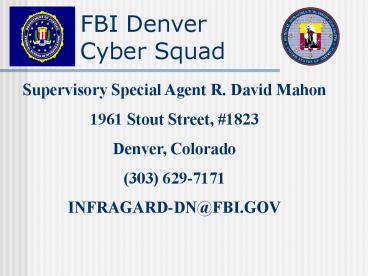
FBI DenverCyber Squad
Supervisory Special Agent R. David Mahon 1961
Stout Street, 1823 Denver, Colorado (303)
629-7171 INFRAGARD-DN_at_FBI.GOV
2
Presidential Decision Directive 63
- The US will take the necessary measures
- to swiftly eliminate significant vulnerability
- to both physical and cyber attacks on our
- critical infrastructures, including our cyber
- systems.
- May 22, 1998
- May 22, 2003
3
Presidential Decision Directive 63
- Increased government security by 2000
- Secure information system infrastructure by 2003
- Federal agencies to serve as model in reducing
infrastructure vulnerabilities - Seeks participation of private industry
4
Executive Office of the President
OSTP (RD)
National Security Advisor
National Coordinator
National Infrastructure Assurance Council
Critical Infrastructure Coordinating Group
National Infrastructure Protection Center
Critical Infrastructure Assurance Office
Sector
Lead Agency
Information Sharing and Analysis Center(s)
The Private Sector
5
PDD 63 Requires the FBI through the NIPC to
- Serve as national infrastructure threat
gathering, assessment, warning, vulnerability
law enforcement investigation/response entity - Be linked electronically as a national focal
point - Establish its own relationships with private
sector - Be the principal means of coordinating US Govt
response, mitigation, investigation and
reconstitution efforts.
6
NIPC Mission
- Detect, deter, warn of, investigate, and respond
to attacks on critical infrastructures
- Coordinate FBI computer intrusion investigations
- Support other agencies and state local
governments involved in infrastructure protection
7
NIPC Mission
- Share, analyze, disseminate information
- Provide training for Federal, state and local
cyber investigators
- Clearinghouse for technological developments
- 24/7 watch and warning capability
8
NIPC Organization
- Location
- Located at FBIHQ in Washington, D.C., the NIPC is
one of the fastest growing investigative areas in
the FBI - Composition
- Multiple government agencies
- Federal, state, and local law enforcement
- Private sector representatives
9
NIPC Programs
10
Key Asset Initiative
11
Key Asset Initiative
- Develop Database for specific entities within
each infrastructure - Key Asset An organization, group of
organizations, system, or group of systems is
considered to be a key asset if it is determined
that the loss of associated goods or services or
information would have widespread and dire
economic or social impact. - Develop Emergency Points of Contact
- Cyber and Physical Threats
- Contingency Planning
- Vulnerability Assessments for Assets with
National Importance
12
Critical Infrastructures
- Critical infrastructures are those physical and
cyber-based systems essential to the minimum
operations of the economy and government.
Presidential Decision Directive-63 May 1998
13
(No Transcript)
14
New Thinking Required To Appreciate
Infrastructure Interdependencies
15
What if...
16
Computer Intrusion Program
17
Vulnerabilities A New Dimension
- Physical vulnerabilities and threats
- are known.
- Cyber vulnerabilities are growing and are not
well understood.
18
New Risks and Threats
- Cyber vulnerability stems from easy accessibility
to infrastructures via Internet
Tools to do harm are widely available and do not
require a high degree of technical skill
Globalization of infrastructures increases
exposure to potential harm
Interdependencies of systems make attack
consequences harder to predict and perhaps more
severe
19
Likely Sources of Attack
81
76
49
31
25
Foreign Competitors
Independent Hackers
CSI/FBI 2001 Computer Crime and Security
Survey Source Computer Security Institute
20
Unauthorized use of computer system within the
last 12 months
64
25
11
Yes
No
Dont Know
CSI/FBI 2001 Computer Crime and Security
Survey Source Computer Security Institute
21
Types of Attacks
26
40
Theft of Proprietary Info System
Penetration Denial of Service Laptop Unauthoriz
ed Access by Insider Insider Abuse of Net
Access Virus
36
64
49
91
94
CSI/FBI 2001 Computer Crime and Security
Survey Source Computer Security Institute
22
Cyber Threats
Unstructured Threats Insiders Recreational
Hackers Institutional Hackers
Structured Threats Organized Crime Industrial
Espionage Hacktivists
National Security Threats Terrorists Intelligence
Agencies Information Warfare
23
Hackers
24
Types of Attacks
- Denial of Service
- Hijacked Domain Names
- Defacement of Web Page
25
Organized Crime Bank Transfers
- In 1994, hackers compromised passwords to
impersonate account holders - Attempted 40 transfers totaling 10 million
- Actual losses of 400,000
- 5 individuals arrested
- All pled guilty to either bank fraud or
conspiracy to commit bank fraud
26
CREDIT CARD EXTORTION
- Russian hackers break into more than 40
e-commerce businesses/databases in 10 states - One business had 38,000 credit-card numbers
compromised another had 15,700 credit cards
numbers stolen - Businesses contacted by subjects they offered
to fix the problem for a price. - And, one victim company hired a hacker as a
computer security consultant!!
27
CREDIT CARD HACKERS
- November, 2000 Undercover sting set
- up in Seattle two subjects lured to US
- Subjects demonstrate their hacking
- prowess for their new employers, then
- arrested on the spot
- 250 gigabytes of stolen data recovered
- through a reverse hack into the
- subjects computers
28
Terrorist Groups
Usama Bin Laden
Aum Shinrikyo
29
Terrorists
- Terrorist fundraising, communications on Internet
- Ramzi Yousef
- Plotted to bomb 11 U.S. airliners in Pacific
- Details of plot encrypted on laptop
- Tamil Tigers web site defacement
- Zapatista National Liberation Army (EZLN)
30
Information Warfare
Several countries have or are developing the
capability to attack an adversarys computer
systems.
Developing a computer attack capability can be
quite inexpensive and easily concealable it
requires little infrastructure, and the
technology required is dual-use. George Tenet,
CIA Director 2/2/99
31
Information Warfare
". . . attaining one hundred victories in one
hundred battles is not the pinnacle of
excellence. Subjugating the enemy's army without
fighting is the true pinnacle of excellence."
Sun
Tzu, The Art of War c. 350 B.C.
Information warfare is the use of, destruction
or manipulation of information on a computer
network to destroy the enemys telephone
network, fuel pipelines, electric grid,
transportation control system, national funds
transfer system. . .in order to achieve a
strategic victory.
--Beijing Jianchuan Zhishi (Chinese Press) 30
June, 1999
32
Ownership of Problem
- Risk is shared among
- public and private interests
Partnership is the Foundation for Infrastructure
Protection
33
INFRAGARD
A Government and Private Sector Alliance
34
(No Transcript)
35
InfraGard Overview
- Voluntary Program/Public and Private
- Sectors
- National Identity, yet Locally Flexible
- Information Shared Locally and
- Nationally
- Fosters Trust Between Members,
- Locally and Nationally
36
Membership Benefits
- Forum for members to communicate
- Prompt dissemination of threat warnings
- Help in protecting computer systems
- Education and training on infrastructure
vulnerabilities - A community that shares information in a trusted
environment
37
Primary Features
- Intrusion Alert Network
- Secure Web Site
- Seminars and training
38
Intrusion Alert Network
- Member sends encrypted message about attack
- to NIPC and FBI Field Office via E-mail
- Detailed description
- Sanitized description
- NIPC transmits sanitized description to
- other members via E-mail
- NIPC analyzes incident
- Trends identified and reported
- Investigation opened if appropriate
39
Secure Web Site
- Information about recent intrusions
- Archives of intrusion incidents
- Original research on security issues
- Chat and conference with other members
- InfraGard news
- Links to other security sites
- Contact information
40
Denver InfraGard Chapter
- Chapter begun November 15, 2000
- Membership from every infrastructure sector
- Quarterly meetings of general membership
- Individual sectors meet more frequently
- Training planned on vulnerabilities, risk
assessment, solutions
41
DENVER INFRAGARD
- CEO/Senior level briefing projects planned
- Educational initiatives underway involving
computer forensic training regional cyber crimes
survey - Action item projects underway with private
sector
42
(No Transcript)
43
IFCC MISSION STATEMENT
- To develop a national strategic plan to address
fraud over the Internet, and to provide support
to law enforcement and regulatory agencies at all
levels of government for crimes that occur over
the Internet.
www.ifccfbi.gov
44
PURPOSE OF THE IFCC
- DEVELOP NATIONAL STRATEGY
- IDENTIFY AND TRACK FRAUD
- ANALYZE INTERNET CRIME TRENDS
- TRIAGE INTERNET COMPLAINTS
- DEVELOP INVESTIGATIVE PACKETS
- FORWARD INFO TO APPROPRIATE AGENCY
www.ifccfbi.gov
45
(No Transcript)
46
(No Transcript)
47
ADVANTAGES WHICH THE INTERNET PROVIDES CRIMINALS
- Identification and Location of
- victims
- Victims do not see or speak to
- fraudsters
- Accepted vehicle for commerce
- Minimal cost to set up web page
- Technology has made Internet
- company set up very easy
www.ifccfbi.gov
48
IFCC INTERNET COMPLAINTS
- 2000 AVG 1,848 PER MONTH
- 2000 TOTAL 14,787
- 2001 AVG 4,155 PER MONTH
- 2001 TOTAL 49,863
- 2002 AVG 5,942 PER MONTH
- 2002 TOTAL 35,657
MAY 8, 2000 THROUGH DECEMBER 31, 2000
JANUARY 1, 2002 THROUGH JUNE 1, 2002
www.ifccfbi.gov
49
Federal Bureau of Investigation
FBI Denver Division Cyber Squad
Tel (303) 629-7171 1961 Stout Street Suite
1823 Fax (303)
628-3240 Denver, Colorado 80294 infragard-dn_at_fbi
.gov