History: - PowerPoint PPT Presentation
Title:
History:
Description:
Bounced checks. Electronic money has same problems. Easy to copy ... In credit card or check transactions, sensitive information is being exchanged. ... – PowerPoint PPT presentation
Number of Views:76
Avg rating:3.0/5.0
Title: History:
1
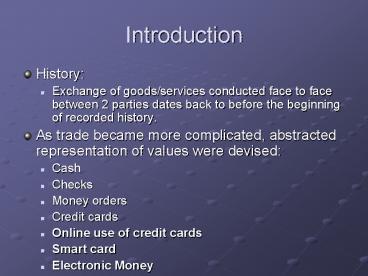
Introduction
- History
- Exchange of goods/services conducted face to face
between 2 parties dates back to before the
beginning of recorded history. - As trade became more complicated, abstracted
representation of values were devised - Cash
- Checks
- Money orders
- Credit cards
- Online use of credit cards
- Smart card
- Electronic Money
2
Problems
- Traditional means of payments
- Counterfeit
- Forged signature
- Bounced checks
- Electronic money has same problems
- Easy to copy
- Digital signature can be reproduced by anybody
who knows the secret cryptographic signing key. - The buyers name is associated with payment
lack of anonymity.
3
Credit Card
- Advantages
- Allows credit
- People can buy more than they can afford
- Widespread but lack
- Anonymity
- Security
- Inability to reach everyone
- In the United States, about 40 of the population
does not have a credit card.
4
- Payment Size
- Macro payments involve large payments from about
10 USD onwards. - Small payments are from 0.1 USD or higher.
- Micro payments can involve fractions of Cents.
- Credit cards too expensive for small/micro
payments - Fixed charge of 2-4.5 (higher on internet)
- The most expensive e-Payment mechanism
- MasterCard 0.29 2 of transaction value
- A 100 charge costs the merchant 2.29
- This cost reflects the security problems
5
Security Problems
- Security problems
- All info is exposed to the merchant
- There is a greater threat over the Internet where
merchants can be located anywhere - All purchases are traceable
6
ePayment - Problems
- Problem
- Banks not set up for instantaneous transactions
- Security
- System design problems
- Keep transaction costs low
- Scale to huge number of transactions (100 billion
per day) - Bank systems (SWIFT, FedWire) do not talk to the
Internet
7
Requirements
- Money atomicity no money is lost or created in a
transfer - Goods atomicity money and goods are exchanged
atomically(both or none) - Non-repudiation No party can deny its role in
the transaction Digital signatures - Desirable Properties
- Universally accepted
- Transferable electronically
- Divisible into change (pay for 10 item with
100 bill) - Forge-proof, Theft-proof
- Private (no one except parties know the amount)
- Anonymous (no one can identify the payor)
- Work off-line (no need for on-line verification)
8
The Participants
- Payer makes the payment. (customer or buyer).
- Payee receives the payment. (merchant or seller).
- Issuer is the third party of the payer, (bank or
service-provider of the payer). - Acquirer is the third party of the payee,
(bank/service-provider of the payee).
- Broker is both issuer and acquirer (when a
protocol requires a single third party to be
shared by payer and payee). - Observer is usually an uninvolved third party
used in the privacy analysis of a payment system.
Observer has information about the transaction.
9
- Certification
- A registration and certification authority for
the management of authentication and symmetric
keys like Kerberos or public keys certification - Arbiter
- To resolves disputes.
- Trusted Third Parties
- Notaries
- To enforce payment receipt notifications,
clearings or witnessing of transactions.
10
Electronic Payment Systems
- Notational Fund Transfer
- Digital Currency
11
Notational Fund Transfer
- In credit card or check transactions, sensitive
information is being exchanged. - For example, you give your credit card to a
merchant, who sends the card number through phone
line and receives confirmation. - Banks meanwhile receive the same information and
adjust buyer's and merchant's accounts
accordingly. - The information being transmitted online in this
case is encrypted for security. - The primary example is the use of digital credit
cards (e.g. CyberCash (www.cybercash.com) and
VISA/MasterCard's SET-based transactions).
12
- The Internet may be more secure than phone lines
for this same old payment methods. (Can you
encrypt your voice when you give your credit card
number over the phone? Can you be sure who the
other person is?)
13
Secure Credit Card
- Most important point in using a credit card for
payments through the Internet is the secure
transmission of the credit card data. - Payer transmits the credit card data or their
equivalent to the payee who submits them in turn
to the acquirer for online validation. - Acquirer resolves the actual payment via the
established financial networks. - The drawback Unsuitability for micro payments.
14
What is ECash
- ECash is the digital analogue to physical coins.
It has the same properties as does the legal
tender to which you're used you can't spend one
coin twice, the coin has no memory of who owned
it or what it was used to purchase, and it's
difficult to forge.
15
- Digital money is created against existing money.
In the long run, digital money may be created on
its own if users accept it on its face value,
which will be determined by how dependable its
issuers are. All monies are only as good as their
issuers. - Very flexible Can be made to behave like
e-checks or anonymous cash as situation warrants.
16
Ecoin
- It is the unit of payment and represents a fixed
amount of money. It is a combination of random
elements chosen by the payer and digital
signatures of the bank.
17
Models of e-cash
- On-line payment means that Bob calls the Bank and
verifies the validity of Alice's token before
accepting her payment and delivering his
merchandise. (This resembles many of today's
credit card transactions.) - Off-line payment means that Bob submits Alice's
electronic coin for verification and deposit
sometime after the payment transaction is
completed. (This method resembles how we make
small purchases today by personal check.)
18
Smart Card
- An electronic device about the size of a credit
card that contains an embedded integrated circuit
(program and memory) - Uses
- Storing digital cash
- Storing information giving hospitals or doctors
personal data without filling out a form - Generating network IDs by storing X.509
certificates, private keys and RSA
crypto-engines establishing your identity when
logging on to an Internet access provider or to
an online bank - Specialized Applications such as SIM (Subscriber
Information Modules) in GSM wireless telephones
-- a SIM contains all the generic information
required to access the telephone network
19
- Smart cards can be typically classified into
broad categories based on how they communicate
with another device - Contact - Direct Communication - the card must be
inserted into a smart card reader which connects
to a conductive module on the card - Connectionless - antenna or other electromagnetic
interface is imbedded in the card - Hybrid cards are dual chip cards with each chip
containing its respective contact or
connectionless interface the chips are not
connected to each other in the card - Combo cards have a single ship with both contact
and connectionless interfaces. - Power for the smart card may be supplied either
by an embedded battery or by a microwave
frequency -- the card needs to be within 2 to 3
inches of the card reader.
20
Smart Card Applications
- Applications
- Ticketless travel Seoul bus system 4M cards, 1B
transactions since 1996 - Authentication, ID
- Medical records
- Ecash
- Store loyalty programs
- Personal profiles
- Government Licenses
- Mall parking . . .
21
- May emerge as the ultimate interface device for
the mobile digital economy. - It will hold your cash, ID information, house and
office keys, subway tokens, all types of
preference files (for house temperature setting,
driver seat setting, etc.) and other information.
- You will exchange these information and digital
products with other people, transact business,
present to police officers, check into a hotel or
a sports arena, and all other things yet to be
imagined.
22
- Over a billion smart cards are in use, primarily
in Europe. Because the current infrastructure in
the US is designed for credit cards with magnetic
strips, there has been a slower rate of adoption
of smart cards in the US. The use of Smart Cards
in Europe received its initial boost from the
French government in 1985 when it purchased 16
million cards for use by its then state-owned
bank.
23
Smart Card Standards
- OpenCard Framework is supported by Sun
Microsystems, IBM, Oracle, Netscape. It is a
standard for NCs, emphasizes portability and
personalization, and adopts Java. - Personal Computer Smart Card (PCSC) Workgroup
Standard is proposed by Microsoft and supported
by Schlumberger Electronic Technologies. - Suns Java Card API, endorsed by Citibank, Visa,
First Union National Bank, VeriFone. - Motorola formed a Smart Card Systems Business
unit for contactless cards using radio.
24
Generic Transaction
- Alice chooses a random x and r and supplies the
bank with B r3f(x)mod n. - The bank returns the third root of B modulo n
r.f(x)1/3 mod n - Alice gives Bob (x, f(x)1/3 mod n)
- Bob calls the bank immediately to verify that the
coin has not been spent.
25
Double Spending
- Bit Sequences can be copied exactly any number of
times. - Alice can copy a Ecoin many times and spend it
repeatedly.
26
Exposing Double Spenders
- To get a coin
- Choose ai, ci, di and ri, 1i k
- Send bank Bi r3.f(xi,yi) mod n, 1i k
- xig(ai,ci) yig(XOR(ai,(uvi)),di).
- Bank chooses k/2 random Bi and sends them.
- For the others, the blinding function must be
revealed. - Bank checks that the values u and v are correct.
- The coin C is extracted
27
Exposing Double Spenders
- To Pay
- Alice sends C to Bob
- Bob chooses a random binary string z1,z2,,zk/2
- Alice responds as follows for all 1 i k
- If zi1 then Alice sends Bob ai, ci and yi
- If zi0 then Alice sends Bob xi, XOR(ai,(uvi))
and di
28
Exposing Double Spenders
- Bob verifies that C is of proper form and Alices
responses fit. - C and Alices responses are sent to the bank
which verifies it and stores ai (for zi1) and
XOR(ai,uivi) (for zi0)
29
Exposing Double Spenders
- If C is used twice, there is a high probability
that for at least one i, ai and XOR(ai, uivi)
is available.
30
Digicash Concept
Merchant
1. Consumer buys Digicash from Bank 2. Bank sends
Digicash bits to consumer 3. Consumer sends
Digicash to merchant 4. Merchant checks with Bank
that Digicash is valid (not already spent) 5.
Bank verifies that Digicash is valid 6. Parties
complete transaction Consumer still has
(invalid) Digicash Anonymous Complex transaction
(checking with Bank) Atomicity a problem
5
4
Bank
3
2
1
Consumer
31
ALICE SEND UNSIGNED BLINDED COINS TO THE BANK
Withdrawal (Minting)
WALLET SOFTWARE
ALICE BUYS DIGITAL COINS FROM A BANK
BANK SIGNS COINS, SENDS THEM BACK. ALICE
UNBLINDS THEM
BOB VERIFIES COINS NOT SPENT
ALICE PAYS BOB
Spending
BOB DEPOSITS
CINDY VERIFIES COINS NOT SPENT
ALICE TRANSFERS COINS TO CINDY
PersonalTransfer
CINDY GETS COINS BACK
32
Micro payment
- If transaction costs can be made low enough to
handle even sub-dollar payments, why should
digital product sellers be limited to accepting
credit card payments and other large-scale
payment methods?
33
Aggregation
- Used when individual transactions are too small
for credit card (e.g. 2.00) - Consumer and Merchant sign up with Aggregator
- Consumer makes purchase. Merchant notifies
Aggregator. - Aggregator keeps Consumers account. When amount
owed is large enough (or every month), charges to
Consumers credit card - Aggregator sends money (less fees) to Merchant
- QPASS, CyberCash, GlobeID